3 OKR examples for Application Security
What are Application Security OKRs?
The Objective and Key Results (OKR) framework is a simple goal-setting methodology that was introduced at Intel by Andy Grove in the 70s. It became popular after John Doerr introduced it to Google in the 90s, and it's now used by teams of all sizes to set and track ambitious goals at scale.
Formulating strong OKRs can be a complex endeavor, particularly for first-timers. Prioritizing outcomes over projects is crucial when developing your plans.
To aid you in setting your goals, we have compiled a collection of OKR examples customized for Application Security. Take a look at the templates below for inspiration and guidance.
If you want to learn more about the framework, you can read more about the OKR meaning online.
Best practices for managing your Application Security OKRs
Generally speaking, your objectives should be ambitious yet achievable, and your key results should be measurable and time-bound (using the SMART framework can be helpful). It is also recommended to list strategic initiatives under your key results, as it'll help you avoid the common mistake of listing projects in your KRs.
Here are a couple of best practices extracted from our OKR implementation guide 👇
Tip #1: Limit the number of key results
Having too many OKRs is the #1 mistake that teams make when adopting the framework. The problem with tracking too many competing goals is that it will be hard for your team to know what really matters.
We recommend having 3-4 objectives, and 3-4 key results per objective. A platform like Tability can run audits on your data to help you identify the plans that have too many goals.
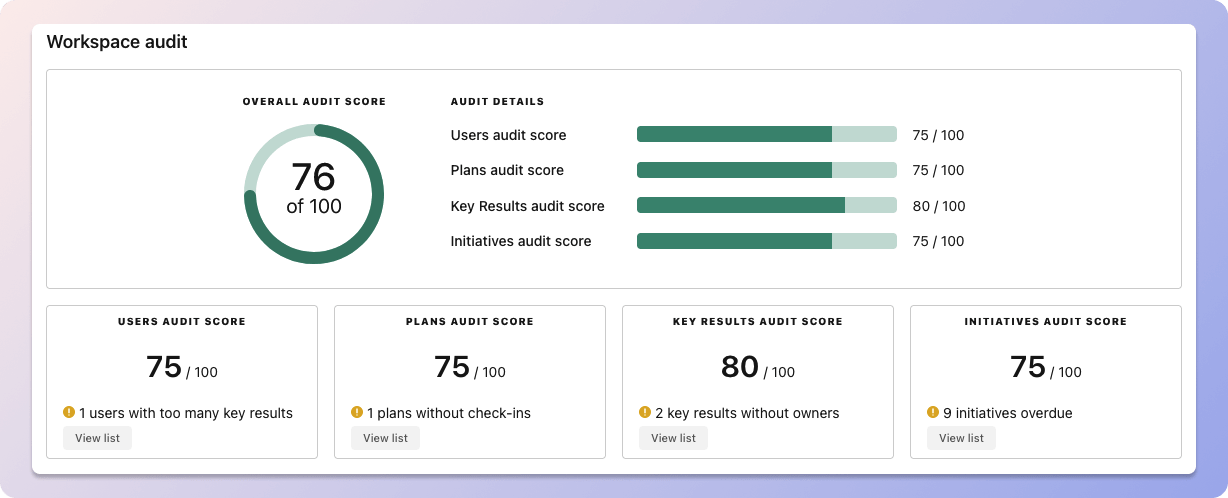 Tability's audit dashboard will highlight opportunities to improve OKRs
Tability's audit dashboard will highlight opportunities to improve OKRsTip #2: Commit to the weekly check-ins
Setting good goals can be challenging, but without regular check-ins, your team will struggle to make progress. We recommend that you track your OKRs weekly to get the full benefits from the framework.
Being able to see trends for your key results will also keep yourself honest.
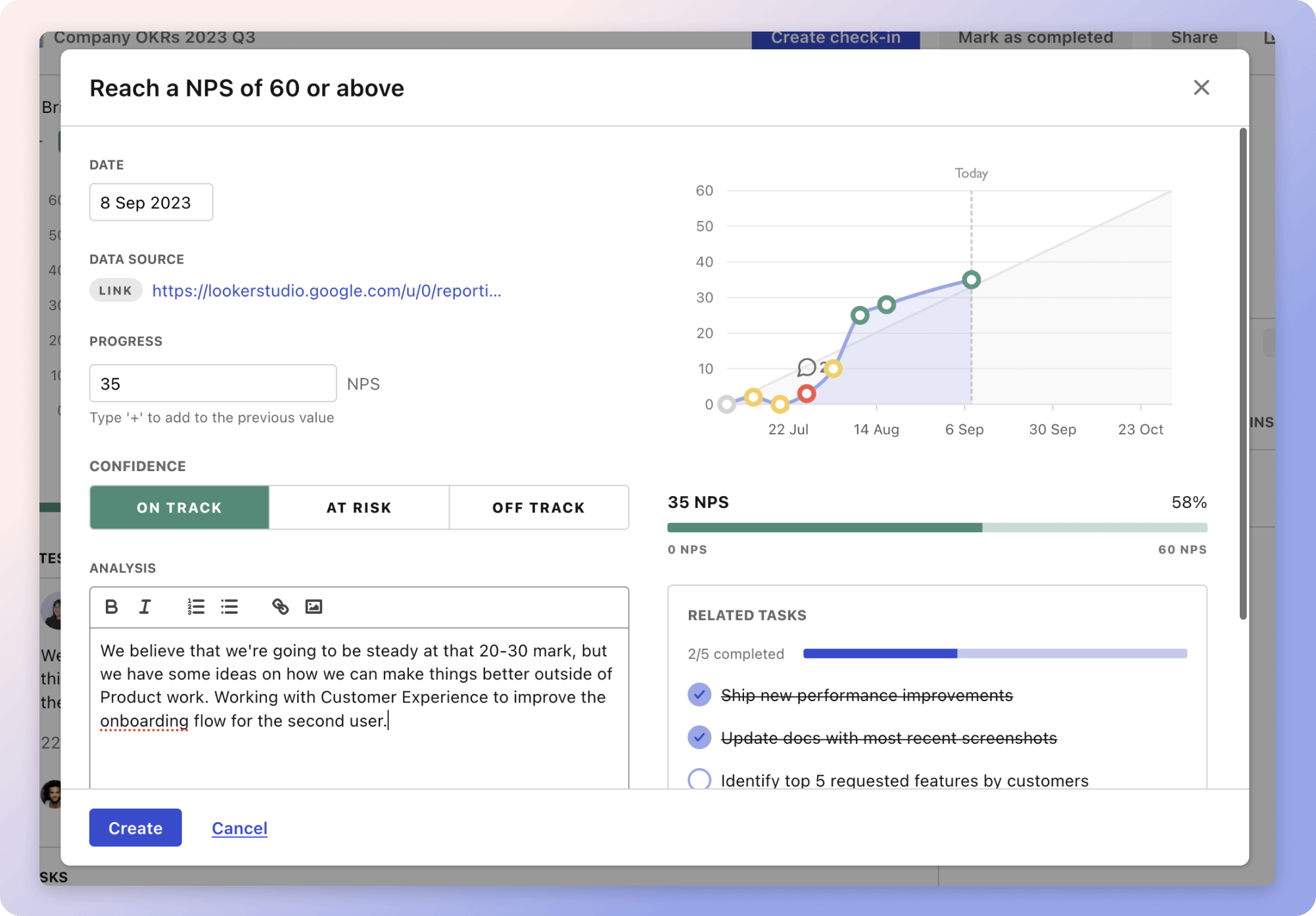 Tability's check-ins will save you hours and increase transparency
Tability's check-ins will save you hours and increase transparencyTip #3: No more than 2 yellow statuses in a row
Yes, this is another tip for goal-tracking instead of goal-setting (but you'll get plenty of OKR examples below). But, once you have your goals defined, it will be your ability to keep the right sense of urgency that will make the difference.
As a rule of thumb, it's best to avoid having more than 2 yellow/at risk statuses in a row.
Make a call on the 3rd update. You should be either back on track, or off track. This sounds harsh but it's the best way to signal risks early enough to fix things.
Building your own Application Security OKRs with AI
While we have some examples below, it's likely that you'll have specific scenarios that aren't covered here. There are 2 options available to you.
- Use our free OKRs generator
- Use Tability, a complete platform to set and track OKRs and initiatives
- including a GPT-4 powered goal generator
Best way to track your Application Security OKRs
Your quarterly OKRs should be tracked weekly in order to get all the benefits of the OKRs framework. Reviewing progress periodically has several advantages:
- It brings the goals back to the top of the mind
- It will highlight poorly set OKRs
- It will surface execution risks
- It improves transparency and accountability
Most teams should start with a spreadsheet if they're using OKRs for the first time. Then, once you get comfortable you can graduate to a proper OKRs-tracking tool.
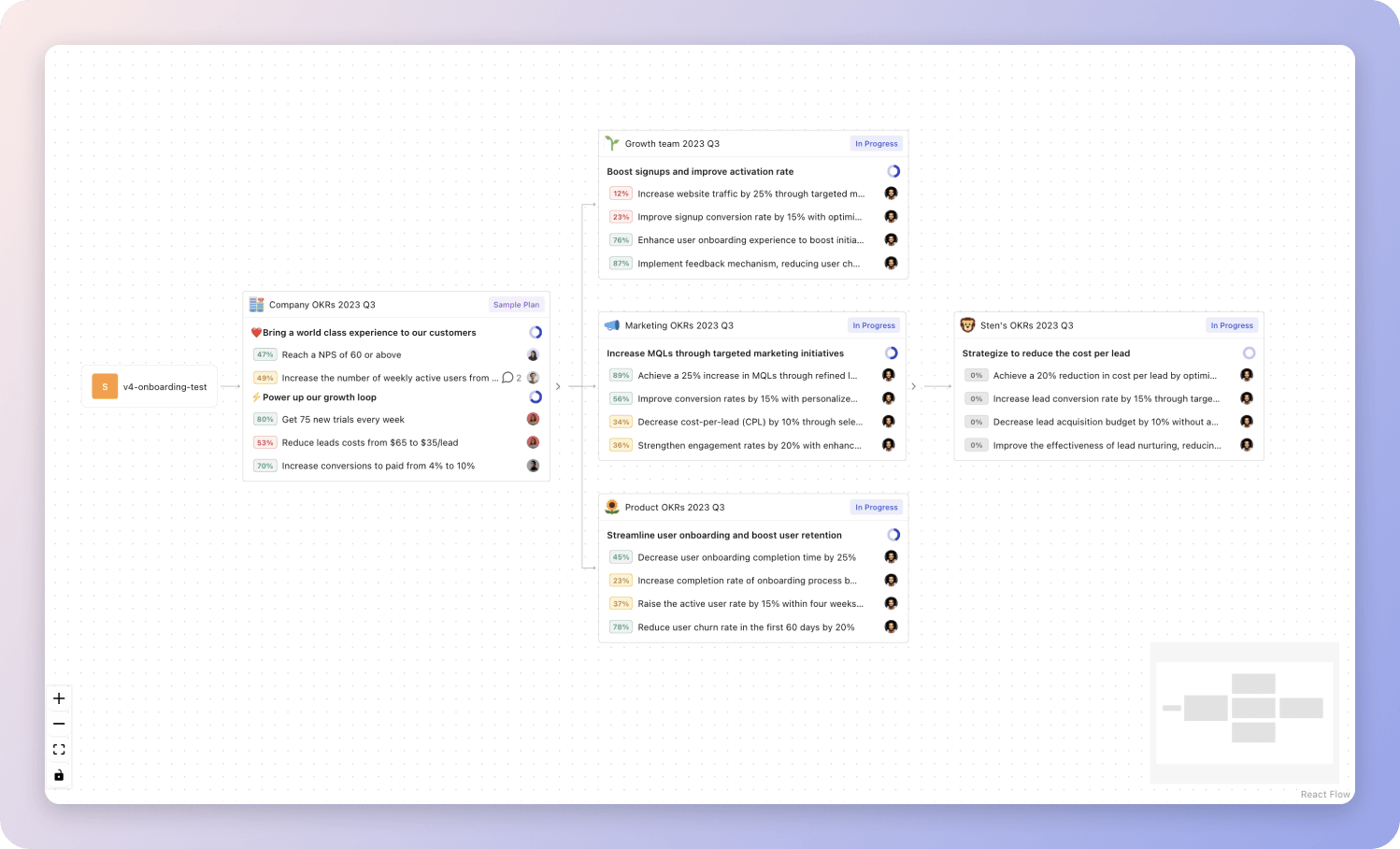 Tability's Strategy Map makes it easy to see all your org's OKRs
Tability's Strategy Map makes it easy to see all your org's OKRsIf you're not yet set on a tool, you can check out the 5 best OKR tracking templates guide to find the best way to monitor progress during the quarter.
Application Security OKRs templates
We've covered most of the things that you need to know about setting good OKRs and tracking them effectively. It's now time to give you a series of templates that you can use for inspiration!
You will find in the next section many different Application Security Objectives and Key Results. We've included strategic initiatives in our templates to give you a better idea of the different between the key results (how we measure progress), and the initiatives (what we do to achieve the results).
Hope you'll find this helpful!
OKRs to enhance application security knowledge and awareness among teams
Improve application security knowledge and awareness
Increase the frequency of security checklist reviews by 50%
Conduct at least one security training session per team
Provide secure coding guidelines and best practices to each team
Implement a mandatory security certification program for all teams
OKRs to successfully complete Micro-segmentation for Tier1 and Tier2 applications
Successfully complete Micro-segmentation for Tier1 and Tier2 applications
Implement micro-segmentation for at least 60% of prioritized applications
Develop a diagram detailing each application's segmentation
Execute approved micro-segmentation plan across identified apps
Identify top 60% of high-priority apps for micro-segmentation
Identify and prioritize all Tier1 and Tier2 applications by end of first month
Evaluate the importance and usage of listed applications
Compile a list of all Tier1 and Tier2 applications
Rank applications based on evaluation results
Develop an individualized micro-segmentation plan for 75% of identified applications
Identify key characteristics of each application for segmentation
Implement segmentation plans on 75% of selected applications
Create customized micro-segmentation strategy for each application
OKRs to successfully migrate all applications to a secure DevOps pipeline
Successfully migrate all applications to a secure DevOps pipeline
Achieve zero security incidents post-migration in the reviewed applications
Regularly review and update security measures
Implement solid security mechanisms post-migration
Conduct thorough security checks and audits before migration
Train 80% of development team on secure DevOps pipeline management
Identify team members needing secure DevOps pipeline training
Organize a training program with a competent instructor
Schedule and implement training sessions for identified members
Implement secure DevOps pipeline framework for 50% of existing applications
Develop or acquire the necessary secure DevOps pipeline framework
Identify applications suitable for secure DevOps pipeline implementation
Roll out the framework across the identified applications
More Application Security OKR templates
We have more templates to help you draft your team goals and OKRs.
OKRs to enhance Product Owners' competency for optimal efficiency
OKRs to optimize vendor management for talent acquisition
OKRs to meet or exceed financial and operational milestones for investor confidence
OKRs to establish monitor arm distribution via furniture dealers
OKRs to expand investor network with five strategic VC firms
OKRs to increase Internal Customer NPS
OKRs resources
Here are a list of resources to help you adopt the Objectives and Key Results framework.
- To learn: Complete 2024 OKR cheat sheet
- Blog posts: ODT Blog
- Success metrics: KPIs examples